Sponsored by Jumio
Sponsored by Illumio
Endpoint Security Effectiveness
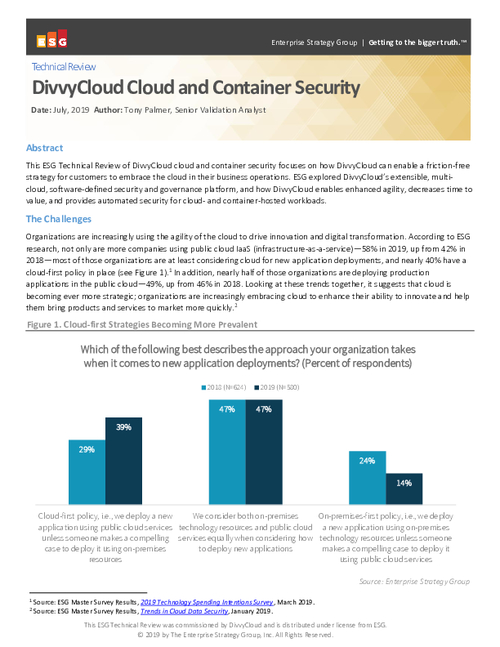
Sponsored by DivvyCloud
DivvyCloud Cloud and Container Security
Sponsored by IBM
The Weaponization of IoT Devices
Sponsored by Optiv & Palo Alto Networks
The SASE Vision: Unifying Zero Trust, CASB & FWaaS
Sponsored by LastPass
Finding an Access Solution for Your Business
Sponsored by Zscaler
Four SD-WAN Security Hurdles to Overcome
Sponsored by Zscaler
Why IT Leaders Should Consider a Zero Trust Network Access Strategy
Sponsored by BlackBerry Cylance
The New Reality: Bring Order to Chaos with Unified Endpoint Security
Sponsored by Hitachi ID Systems, Inc.
5 Questions Every CIO Must Answer in the Coronavirus Age
Sponsored by Tanium
From Chaos to Clarity to Control
Sponsored by Zscaler
Network and Security Transformation - Enabling your Digital Business
Sponsored by HID Global