Sponsored by Experian
Sponsored by Webroot
PassMark Ranks Leading Endpoint Protection Products
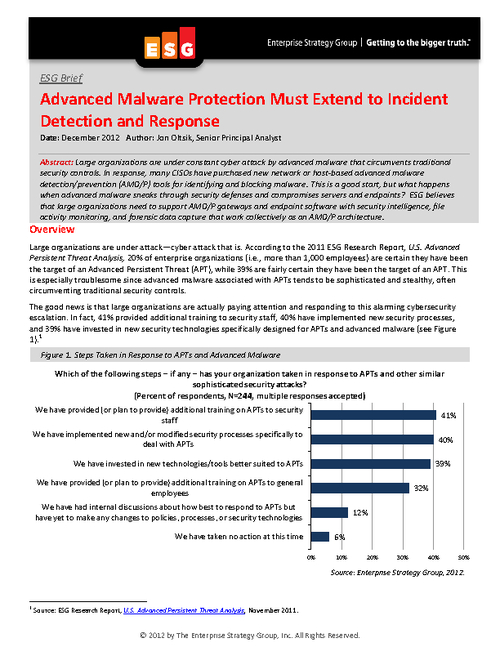
Sponsored by Sourcefire Network Security
What's Your Organization's Plan When Malware Sneaks in?
Sponsored by SpectorSoft Corporation
Six Obvious Threats to Data Security You Haven't Really Addressed
Sponsored by Ipswitch File Transfer
Are Employees Putting Your Company's Data at Risk? [eBook]
Sponsored by Dell SecureWorks
How to Defend Against Advanced Persistent Threats
Sponsored by Guidance Software
How 3 Cyber Threats Transform the Role of Incident Response
Sponsored by Trend Micro
VDI-Centric Endpoint Security Lowers Costs and Increases ROI
Sponsored by HP & Intel
Strategy Guide to Business Risk Mitigation for Financial Services
Sponsored by HP & Intel
Business Risk and the Midsize Firm: What Can Be Done to Minimize Disruptions?
Sponsored by nuBridges, Inc.
Protect Personally Identifiable Information (PII) as if Your Business Depends on It
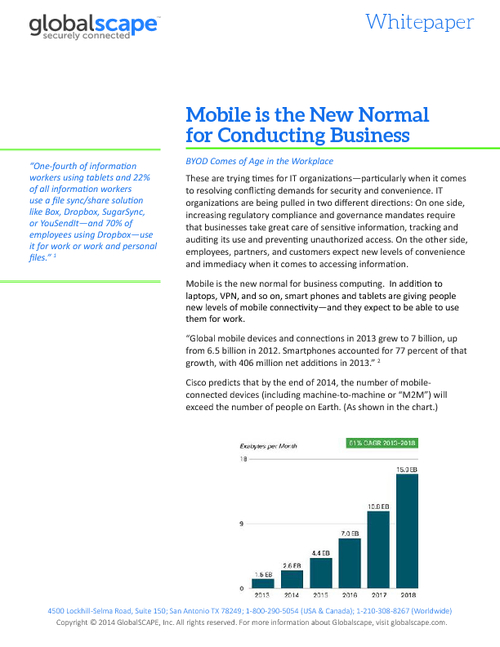
Sponsored by GlobalSCAPE
Mobile is the New Normal for Conducting Business
Sponsored by Symantec