Sponsored by Symantec
Sponsored by Dell
Understanding Pass-the-Hash Attacks - and Mitigating the Risks
Sponsored by Informatica
Ponemon Institute Survey Report: Top Enterprise Threats to Data Security
Sponsored by Damballa
Q2 2014 State of Infections Report
Sponsored by Sourefire, LLC
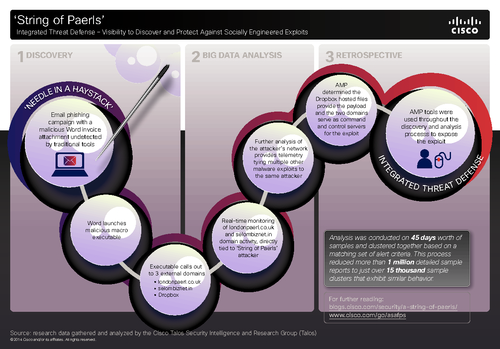
Integrated Threat Defense - Visibility to Discover and Protect Against Socially Engineered Exploits
Sponsored by Sourefire, LLC
Case Study: Making Threat Protection More Intelligent and More Accurate
Sponsored by BitSight
Information Security Risk and the Need for Quantitative Ratings
Sponsored by BitSight
Securosis: Threat Intelligence for Ecosystem Risk Management
Sponsored by Sourefire, LLC
Threat-Focused Next-Generation Firewall
Sponsored by Palo Alto
Application Usage and Threat Report
Sponsored by Palo Alto
The 2014 Firewall Buyers Guide
Sponsored by Palo Alto
Are You Still Using Proxies For URL Filtering? There Is a Better Way
Sponsored by Palo Alto Networks
Cybersecurity for Dummies eBook
Sponsored by Palo Alto
Cybersecurity Imperatives: Reinvent your Network Security
Sponsored by Palo Alto