Sponsored by IBM
Sponsored by IBM
Get Smart to Shut Down Insider Threats
Sponsored by AccessData
The Regulatory Climate Around the World: Best Practices for Global Compliance
Sponsored by AccessData
Do the Benefits of Personal Devices at Work Outweigh the Drawbacks?
Sponsored by AccessData
Supplementing the Security Limitations in Office 365
Sponsored by Akamai
How to Fix the Hole in Your Enterprise Security Strategy
Sponsored by Akamai
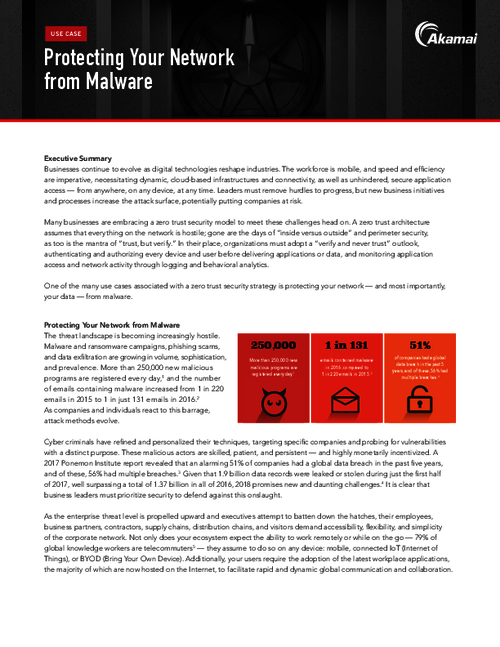
Protecting Your Network from Malware
Sponsored by Akamai
Adopt DNS Best Practices to Proactively Protect Against Malware
Sponsored by Akamai
Cybercrime by the Numbers
Sponsored by Akamai
Is DNS Your Security Achilles Heel?
Sponsored by Akamai
5 Reasons Enterprises Need a New Access Model
Sponsored by Akamai
Remote Access Redefined: Managing the Rise of Third-Party Users
Sponsored by Akamai