Sponsored by Solutionary
Sponsored by Solutionary
Top-Down Security and the Security Life Cycle
Sponsored by Solutionary
Malware Detection with Network Monitoring: Not Quite Enough
Sponsored by FireEye
Gazing Into the Cyber Security Future: 20 Predictions for 2015
Sponsored by FireEye
Siloed Security: Real World Examples of How Attackers Exploit the Gaps
Sponsored by FireEye
The Numbers Game: How Many Alerts is too Many to Handle
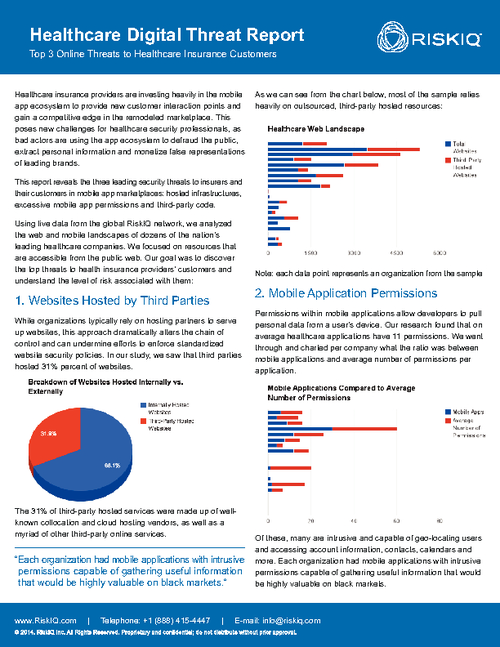
Sponsored by RiskIQ
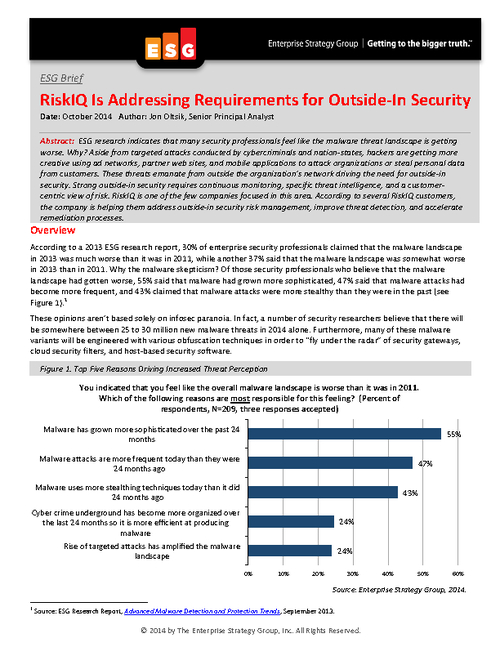
Malware Attack Trends: More Sophisticated, More Frequent
Sponsored by RiskIQ
Top Five Malvertising Threats
Sponsored by RiskIQ
Top Three Online Threats to Healthcare Organizations
Sponsored by General Dynamics Fidelis Cybersecurity Solutions
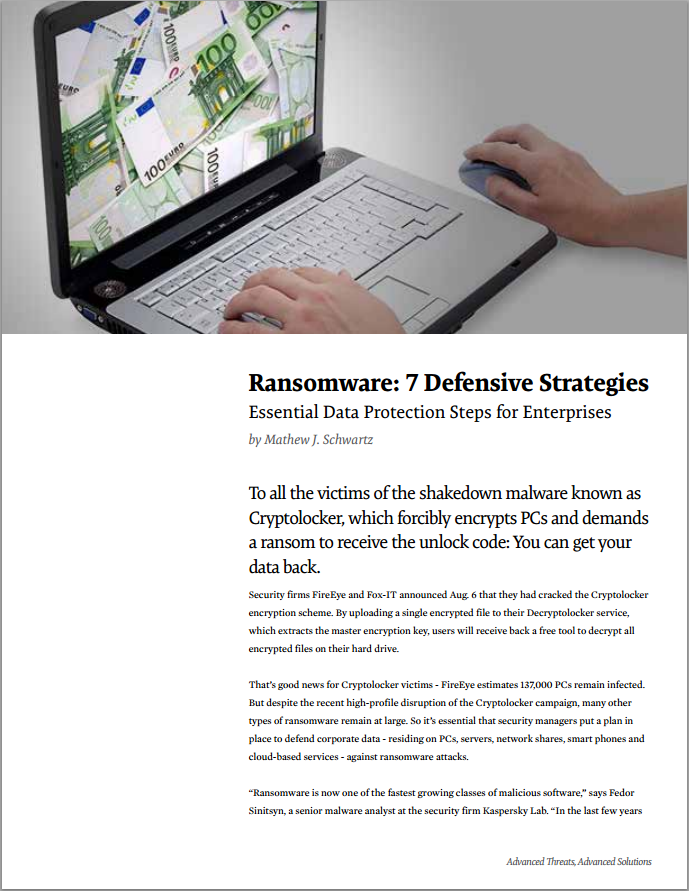
Advanced Threats, Advanced Solutions
Sponsored by General Dynamics Fidelis Cybersecurity Solutions
Ransomware: 7 Defensive Strategies
Sponsored by GlobalScape
4 Keys to Protecting Businesses from Downtime
Sponsored by GlobalScape
Business Continuity: Leveraging High Availability Clustering
Sponsored by GlobalScape
Multifactor Authentication
Sponsored by GlobalScape