Sponsored by Agari
Sponsored by Venafi
Buyer's Guide for Certificate Management
Sponsored by Venafi
Digital Certificates: Next Generation Identity Access Management
Sponsored by Venafi
The Machine Identity Crisis:The Security of Machine-to-Machine Communications
Sponsored by Venafi
Dark Web Research: How Much Will Criminals Pay for Your Certificates?
Sponsored by Venafi
4 Steps to SSH Security: Protect Privileged Access
Sponsored by Venafi
Stop Unauthorized Abuse of Privileged Access: Protect your SSH Keys
Sponsored by HyTrust and Intel
Average Cost of Healthcare Breach? $3.62 Million, Regardless of Compliance
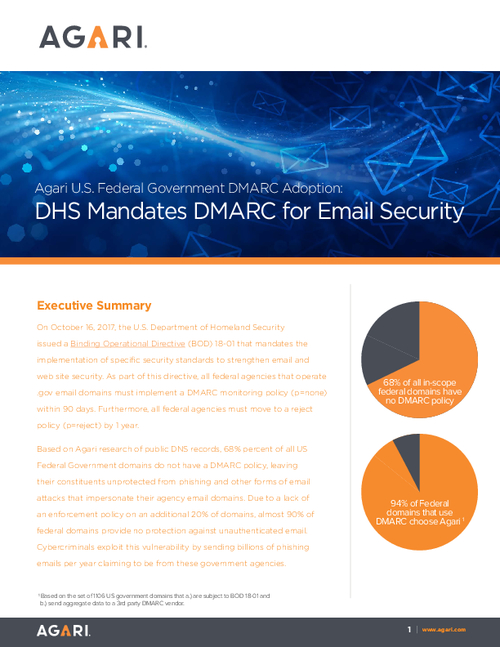
Sponsored by Agari
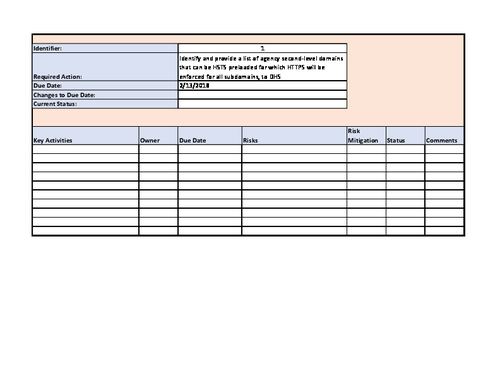
Federal: Getting Started with DMARC
Sponsored by Agari
Federal DMARC Adoption Report
Sponsored by Bricata
Preventing Attacks from Spreading
Sponsored by Carbon Black
2017 Next-Generation Endpoint Security Vendor Landscape
Sponsored by Citrix
Ransomware: Four Ways to Protect Data Now
Sponsored by Citrix
Addressing Today's Endpoint Security Challenges
Sponsored by Trend Micro