Sponsored by HID Global
Sponsored by HID Global
Unlocking Possibilities: Safeguarding Cyber Networks
Sponsored by HID Global
When One Door Opens: An Apple Wallet Badge Unlocks Many
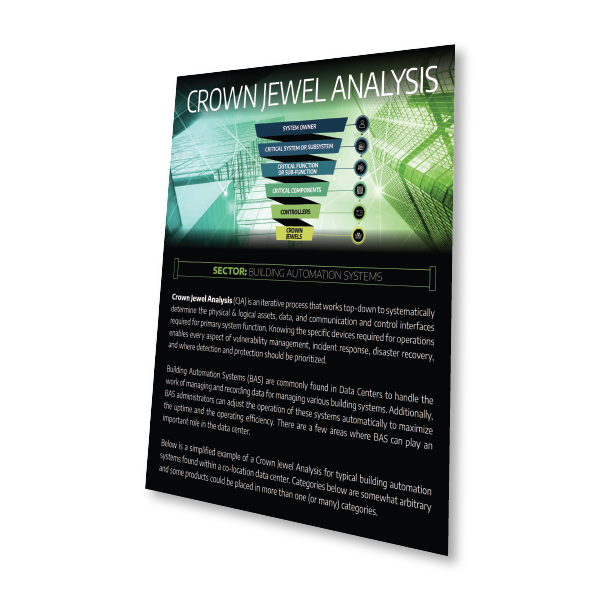
Sponsored by Dragos
Infographic | Crown Jewel Analysis for Building Automation Systems
Sponsored by Dragos
Preparing for and Responding to OT Security Incidents in Industrial Environments
Sponsored by Rockwell Automation
Un-Blurring the Lines Between IT and OT Cybersecurity
Sponsored by Fortra
Navigating Industrial Cybersecurity: A Field Guide
Sponsored by Cyberark
Securing Identities Across the Software Supply Chain and Development Environments
Sponsored by Zoho & ManagEngine
Endpoint Security Essentials for C-Suites
Sponsored by Zoho & ManagEngine
Endpoint Security Essentials for C-Suites
Sponsored by Dragos
How Dragos Activity Groups Obtain Initial Access Into Industrial Environments
Sponsored by Tanium
What You Don't Know Can Hurt You: Expert Advice on Measuring Risk
Sponsored by Splunk
Bridging the Data Divide
Sponsored by Incognia