Sponsored by Tenable
Definitive Guide to Continuous Network Monitoring
Sponsored by Arbor Networks
Breach Prevention: Hunting For Signs of Compromise
Sponsored by Level 3
Cybersecurity- You're Already Compromised
Sponsored by IBM
Indicators of Compromise: Forensics of a Breach
Sponsored by FireEye
Finding Alerts that Lead to Compromise
Sponsored by IBM
Stopping Zero-Day Exploits for Dummies
Sponsored by IBM
Dating Apps Vulnerabilities & Risks to Enterprises
Sponsored by IBM
Managing Security Risks and Vulnerabilities
Sponsored by BitSight
Continuous Third Party Security Monitoring: Forrester Report
Sponsored by Solutionary
Malware Detection with Network Monitoring: Not Quite Enough
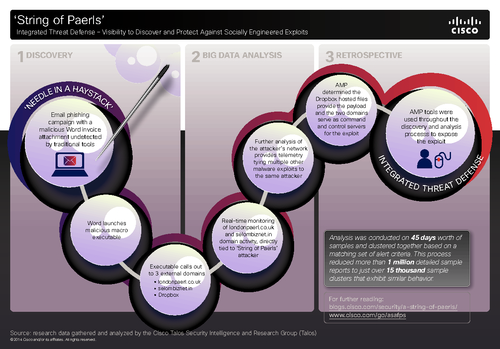
Sponsored by Sourefire, LLC
Integrated Threat Defense - Visibility to Discover and Protect Against Socially Engineered Exploits
Sponsored by SpectorSoft
Implementing an Employee Monitoring Program
Sponsored by SpectorSoft