Application Security & Online Fraud , Governance & Risk Management , IT Risk Management
TikTok App Had Major Security Vulnerabilities
Now Fixed, Check Point Says Flaws Could Have Led to Account Takeover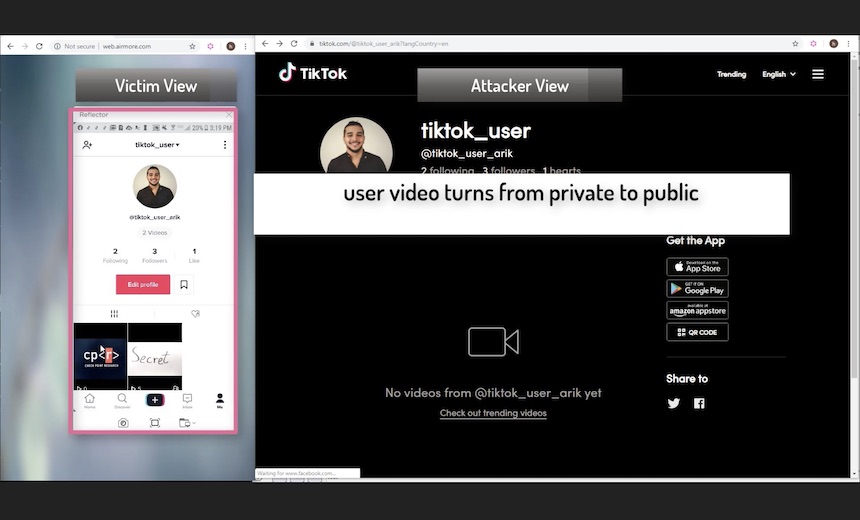
The security company Check Point has revealed several vulnerabilities in TikTok, the popular Chinese video app that has raised concerns lately from the U.S. military and lawmakers.
See Also: State of the Internet/Security Report: API: The Attack Surface That Connects Us All
Check Point says it found a range of vulnerabilities, including the ability to send TikTok users malicious links, view sensitive account data and even delete or add content to a user's account.
“TikTok videos are entertaining,” Check Point writes in a blog post with its technical findings. “But as some have experienced, there is often a fine line between fun clips to private, even intimate assets being compromised while trusting to be under the protection from the apps we use. The research presented here shows the risks associated with one of the most popular and widely used social apps in the world.”
TikTok says it has confirmed with Check Point that the vulnerabilities have been fixed. Check Point says it reported the issues to TikTok on Nov. 20 and Tiktok fixed them by Dec. 15.
"TikTok is committed to protecting user data. Like many organizations, we encourage responsible security researchers to privately disclose zero day vulnerabilities to us,” says Luke Deshotels of TikTok’s security team.
NatSec Threat?
In October, U.S. lawmakers raised questions over whether TikTok was a risk to national security. Last month, the Defense Department called for military personal to uninstall it from government-issued phones, and the U.S. Army and Navy have banned the app (see: US Army Follows Navy in Banning TikTok App: Report).
TikTok is owned by Beijing-based ByteDance Technology. The U.S. has been increasingly distancing itself from Chinese technology companies, such as Huawei, for fears that using their products would offer inroads to spying. The U.S. has also called out alleged Chinese hacking, filing indictments against members of the Chinese military (see: FCC Takes Steps Toward Squeezing Out Huawei, ZTE).
One of TikTok's vulnerabilities was startingly simple: Its main website allowed users to send an SMS to another user with a link to download the app.
By capturing the HTTP traffic with a tool such as Burp suite, it was possible to change out that link to a malicious domain. That’s an especially powerful type of attack as the popularity of TikTok continues to grow.
Check Point found another serious flaw that allowed for redirecting users to malicious websites. It was possible to tack on a malicious website to a legitimate login link that came from TikTok’s domain, Check Point writes.
“The redirection process was found to be vulnerable, since the validation regex is not validating the value of the redirect_url parameter properly,” the researchers write. “Rather, the regex validates the parameter value ending with tiktok.com., making it possible to perform a redirection to anything with tiktok.com.”
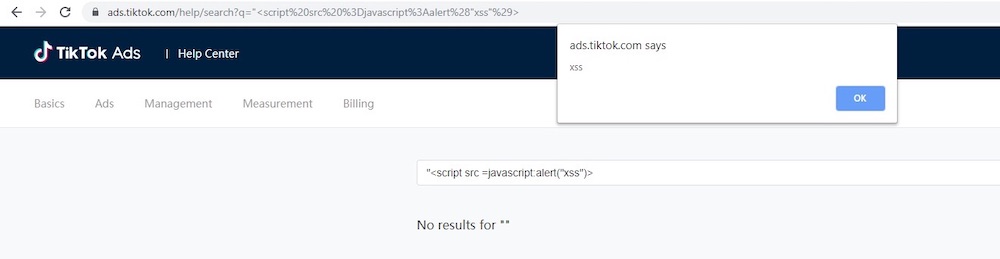
XSS, CSRF
Those flaws opened up other possible attacks due to other TikTok vulnerabilities, including cross-site scripting and cross-site request forgery, Check Point says.
“With the lack of anti-cross-site request forgery mechanism, we realized that we could execute JavaScript code and perform actions on behalf of the victim, without his/her consent,” they write.
With a victim’s cookies in hand, it was possible to send am HTTP GET request and delete a user’s video in a cross-site request forgery attack. Check Point also found they could create a video on their own account but then post it to the victims via a HTTP POST request.
Other shenanigans were possible as well, such as forcing a victim’s account to approve the attacker as a follower and changing the privacy settings of a video from private to public.
There were also cross-site scripting flaws that led to the extraction of sensitive personal information using JavaScript against two APIs, Check Point writes.
TikTok uses two security policies, Cross Origin Resource Sharing, or CORS, and Same Origin Policy, or SOP, to help prevent mischief. But Check Point found an error in how those policies were implemented.
“We found out that TikTok had implemented an unconventional JSONP callback that provides a method to request data from API servers without CORS and SOP restrictions,” Check Point writes. “Bypassing those security mechanisms allowed us to steal all the sensitive information of the victims by triggering an AJAX request to the JSONP callback, resulting in JSON data wrapped by JavaScript function.”
The personal data accessible included email addresses, payment information and birth dates, according to Check Point.