Enterprise Mobility Management / BYOD , Governance & Risk Management
Report Spells Out Medical Device Risks
Makes Recommendations for Boosting Cybersecurity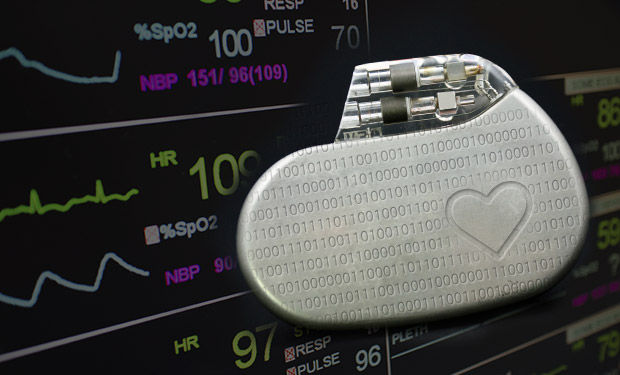
A new report by Atlantic Council think tank and Intel Security serves as a reminder about the importance of medical device cybersecurity. But it's also a wake-up call for healthcare organizations to seriously consider consumer wearable health devices in their risk management strategies.
See Also: ZTNA Buyer's Guide
The report, The Healthcare Internet of Things: Rewards and Risks, outlines the security and privacy risks for four categories of networked medical devices. It makes several recommendations, including addressing medical device cybersecurity in the early stages of product development.
The four types of devices addressed in the report are: consumer products for health monitoring, such as Fitbit and Nike FuelBand; wearable external medical devices, including portable insulin pumps; internally embedded medical devices, such as pacemakers; and stationary medical devices, both hospital-based, such as chemotherapy dispensing stations, and home-based, including cardio-monitoring gear.
"Networked medical devices raise four main and overlapping areas of concern: accidental failures, privacy violations, intentional disruption and widespread disruption," the report states.
The study also notes that nearly half of healthcare providers that were polled in a recent PricewaterhouseCoopers global survey said they have integrated consumer technologies, such as wearable health-monitoring devices or operational technologies like automated pharmacy-dispensing systems, with their IT ecosystems.
"Medical devices - especially in the consumer personal-fitness space - already stream data to cloud servers, which can be in another jurisdiction that might have significantly different health and privacy regulations," the report notes.
With consumer devices like Fitbit and, soon, the Apple Watch generating health information that patients want to share with their healthcare providers, organizations need to be thinking about how to safeguard that data if they use it in the treatment of those with chronic illnesses or other health issues, some security experts say.
"Many of these consumer wearable devices and apps are still very new, and they're often seen more as being 'cute' rather than 'serious medicine'," says Jason Healy, a co-author of the report. He's director of the Cyber Statecraft Initiative at Atlantic Council, a think tank that focuses on leadership and engagement in international affairs. "So the good news is that we're probably a couple years away before these devices get scaled for the use in serious medical care. That gives healthcare providers and regulators time before this becomes an issue," he tells Information Security Media Group.
Healthcare provider organizations that are considering collecting and using data generated by wearable medical devices need to take extra precautions to safeguard this data, says security expert Mac McMillan, founder of consulting firm CynergisTek.
"Healthcare entities should employ sound selection processes to understand the risks associated with the devices," he says. "They should seek those [devices] that are most secure as it relates to basic design factors such as operating system, patching, access controls, etc."
Key Recommendations
The new report makes several recommendations for how data security and privacy for the Internet of Things can be improved.
"As with security challenges accompanying other new technologies, open collaboration and communication are key to managing and reducing risk," the report notes. "This includes collaboration and communication among regulators, as well as between regulators, industry and medical and healthcare practitioners."
The study recommends:
- Stressing security at the outset of product development, manufacture and use, rather than as an afterthought;
- Improving private-private and public-private collaboration;
- Moving toward evolutionary change of the regulatory approval paradigm for medical devices;
- Engaging patients and their families in discussions about cybersecurity and medical devices.
Other Warnings
The Atlantic Council/Intel Security report isn't the first that's spotlighted the security and privacy risks associated with medical devices, including consumer wearable gear. A recent report from the Federal Trade Commission also noted that as the use of wearable fitness devices, health applications and interconnected medical devices expands, organizations need to take steps to protect the privacy and security of consumer data that these products collect, store and transmit (see FTC on Consumer Health Device Risks).
Among the security risks these devices pose are enabling unauthorized access and misuse of personal information for ID theft, fraud, and other crimes; facilitating attacks on other systems; and creating consumer safety risks, the FTC noted.
Healthcare organizations have a long way to go in terms of shoring up their medical device cybersecurity, based on findings from the recent 2015 Healthcare Information Security Today survey of senior security and privacy leaders. That soon-to-be-released ISMG survey found that only 40 percent of organizations had implemented formal security policies and procedures for medical devices. And only 8 percent have implemented formal security policies and procedures for wearable devices, such as FitBit.
The Atlantic Council/Intel Security study also notes that the PwC medical device security survey found that only 59 percent of surveyed healthcare organizations had performed even a rudimentary risk assessment of the networked medical devices or technologies.
Moves to Make
The Food and Drug Administration has been pushing manufacturers to consider the cybersecurity of their medical devices in the full life cycle of their products, including in the design and development phase (see Ramping Up Medical Device Cybersecurity).
In a recent interview, Michael McNeil, global product security and services officer at Philips Healthcare, described a four-prong strategy of how that company is securing its medical devices.
That strategy includes a risk assessment process for all of the company's medical device product releases, "where we are tracking the very high vulnerabilities and putting together appropriate remediation plans," he says. "This should allow us to ultimately remove any vulnerabilities within our environment, as we look at items such as unpatched systems, default passwords and encryption not being in place."