Anti-Phishing, DMARC , Email Threat Protection , Fraud Management & Cybercrime
Microsoft Details Yearlong Office 365 Phishing Campaign
Researchers Found Hackers Deploying Morse Code to Help Evade Detection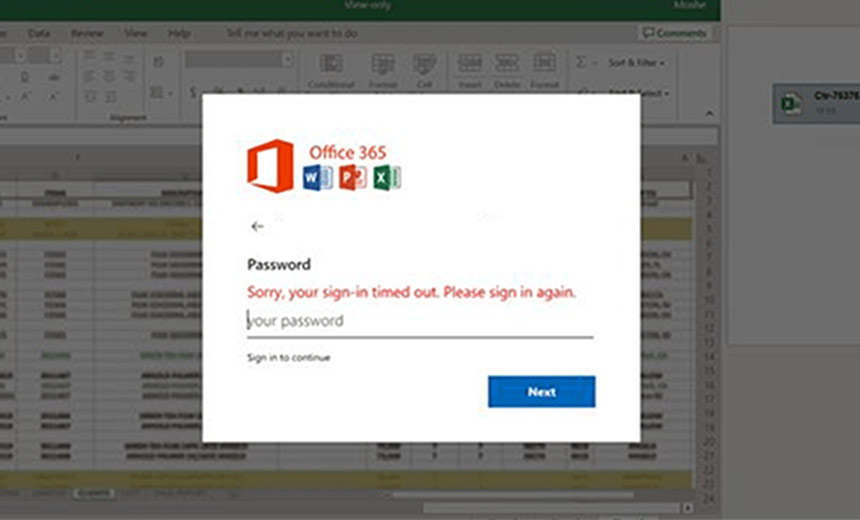
A yearlong phishing campaign used various techniques, including deploying Morse code in some cases, to help evade security tools while attempting to harvest the credentials of Office 365 users, according to a report published by Microsoft researchers this week.
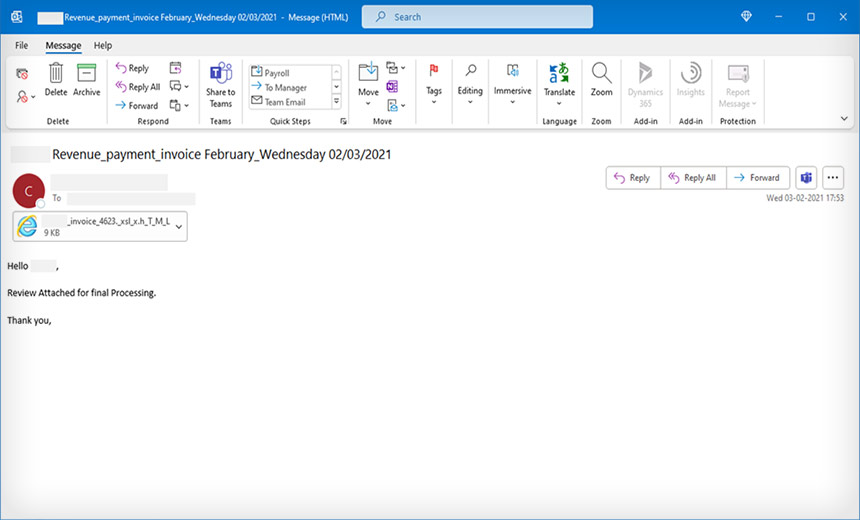
As part of this phishing campaign, the attackers deployed a variety of techniques and tools to create realistic-looking phishing emails that appear to resemble invoices with Microsoft Excel HTML spreadsheets attached. If a user opened one of these malicious attachments, the group behind the attack could harvest their Office 365 credentials as well as other details, such as the device's specific IP address and location.
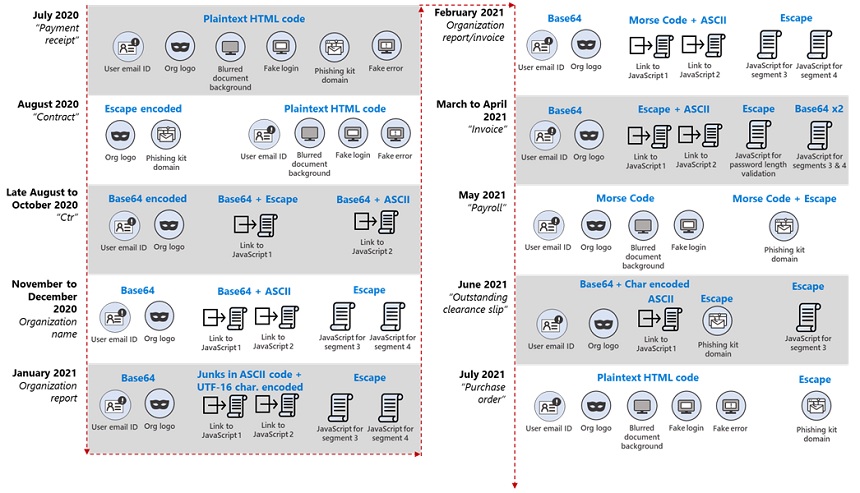
During the year, the Microsoft researchers found that the attackers behind the campaign changed their tactics and techniques, including obfuscation and encryption mechanisms, about every 37 days on average to help avoid detection by security teams.
The researchers also found the attackers broke the HTML files into multiple segments, which helped make the code look benign to security tools.
"In effect, the attachment is comparable to a jigsaw puzzle: On their own, the individual segments of the HMTL file may appear harmless at the code level and may thus slip past conventional security solutions," the Microsoft researchers note in the report. "Only when these segments are put together and properly decoded does the malicious intent show."
The Microsoft report noted that the phishing attacks appeared active through at least July, but the researchers did not identify the group behind the campaign. It's also not clear how successful these malicious emails have been at stealing credentials, but the use of social engineering techniques shows the attackers are persistent.
"This campaign's primary goal is to harvest usernames, passwords, and - in its more recent iteration - other information like IP address and location, which attackers use as the initial entry point for later infiltration attempts," according to Microsoft. "The campaign components include information about the targets, such as their email address and company logo. Such details enhance a campaign's social engineering lure and suggest that a prior reconnaissance of a target recipient occurs."
Techniques
The Microsoft researchers found that the phishing emails appear to the reader as fairly benign and routine - typically mimicking business-related transactions or a vendor invoice. In most cases, the messages had an HTML file attached, designed to look like an Excel spreadsheet, the report notes.
When the victim opens the attachment, it launches a browser window and displays a fake Office 365 credentials dialog box on top of a blurred Excel document. This dialog box typically displays details about the organization the intended victims work for, such as their email address and - in some instances - the company logo.
It's this dialogue box that prompts the victim to input his or her username and password, which are then harvested and sent back to the attackers, the report notes.
"If the user enters their password, they receive a fake note that the submitted password is incorrect. Meanwhile, the attacker-controlled phishing kit running in the background harvests the password and other information about the user," the researchers say.
When examining the phishing emails, the researchers found that the HTML code could be broken down into separate segments, which helped bypass security tools and avoid detection. These segments include:
- Segment 1: This contains the email address of the intended target or victim.
- Segment 2: This contains the logo of the targeted organization, which is pulled from various repositories. If no logo is available, it will default to Office 365.
- Segment 3: This is a script that loads an image of a blurred document, indicating that sign-in has supposedly timed out.
- Segment 4: This is the script that prompts the user to enter their password, submits the entered password to a remote phishing kit and displays a fake page with an error message to the user.
The researchers also note that the attackers kept changing the code and the obfuscation techniques. This has happened at least 10 times since the phishing campaign began, starting in July 2020 and continuing through at least last month.
Dirk Schrader, the global vice president for security research at New Net Technologies, notes that the constantly changing tactics, along with the use of HTML code, makes spotting this particular phishing campaign difficult unless all messages with HTML code attachments are quarantined immediately.
"As the camouflage changes quite frequently, the best options for the organization are to look for HTML-based file attachments, redirect those into a quarantine zone should the exchange of that kind of attachments be a valid part of the business processes - with an automated notification of the user to verify sender and case - or filter them completely," Schrader says.
Morse Code
When the Microsoft researchers looked at the February iteration of the phishing campaign, they found that the encoding technique had changed to incorporate Morse code dots and dashes as a way to hide the encryption. Specifically, the attackers used JavaScript to help hide the ASCII code as part of this technique.
"Morse code is an old and unusual method of encoding that uses dashes and dots to represent characters. This mechanism was observed in the February ('Organization report/invoice') and May 2021 ('Payroll') waves," according to Microsoft. "In the February iteration, links to the JavaScript files were encoded using ASCII then in Morse code."
Bleeping Computer first reported on some phishing emails using Morse code in February.
John Bambenek, a threat intelligence advisor at the security firm Netenrich, says these techniques, especially the use of Morse code, show that these phishing emails can bypass traditional techniques such as blacklisting and that more sophisticated defenses are needed.
"If we rely on blacklisting techniques, there are near-infinite ways to obfuscate and code away detection of malicious behavior," Bambenek says. "Ideally, we should focus on detecting what is benign and anything outside of that, such as the use of Morse code - which only would be used by a ham radio operator, of course - should be flagged or blocked."