Security Agenda 2012: The Year of Mobile Security
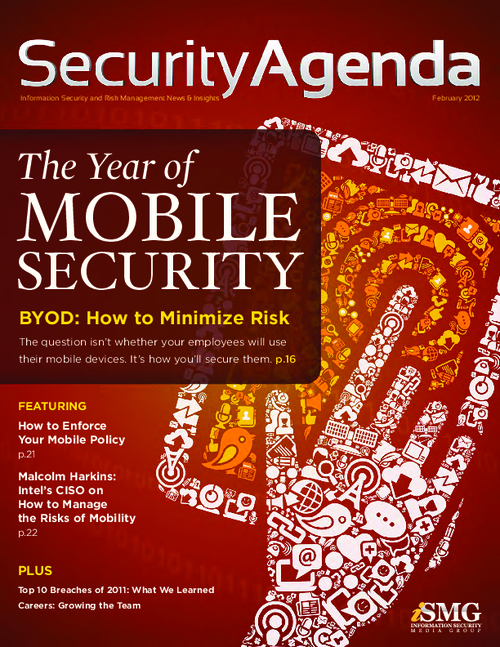
The bring-your-own-device phenomenon has swept global businesses, and the challenge only intensifies with every new wave of smart phones, tablets and portable storage devices.
It's no longer a question of whether organizations will allow employees to use their own mobile devices. That's already happening.
The real question is: How will you secure their usage?
Mobile security is the cover story of this 2012 edition of Information Security Media Group's Security Agenda - our annual overview of the year's top priorities. Included in this feature package are:
- BYOD: How to Minimize Risk
- How to Enforce Your Mobile Policy
- Intel's CISO on Managing the Risks of Mobility
Beyond mobility, we also present a variety of features on other key topics facing security and risk management leaders in 2012.