GAO: Agencies Show Persistent Cybersecurity Weaknesses
Report Also Questions Completeness of Guidance Inspectors General Receive
A new report from the Government Accountability Office points out persistent cybersecurity weaknesses among the federal government's two dozen largest agencies. The GAO contends these weaknesses illustrate the challenges agencies face in effectively applying information security policies and practices.
The report, Agencies Need to Correct Weaknesses and Fully Implement Security Programs, also questions the comprehensiveness of the guidance the White House Office of Management and Budget and Department of Homeland Security provide inspectors general for auditing the IT security compliance of agencies.
"Federal agencies' information and systems remain at a high risk of unauthorized access, use, disclosure modification and disruption," Gregory Wilshusen, GAO's information security issues director, says in the report. "These risks are illustrated by the wide array of cyber threats, an increasing number of cyber incidents and breaches of [personally identifiable information] occurring at federal agencies."
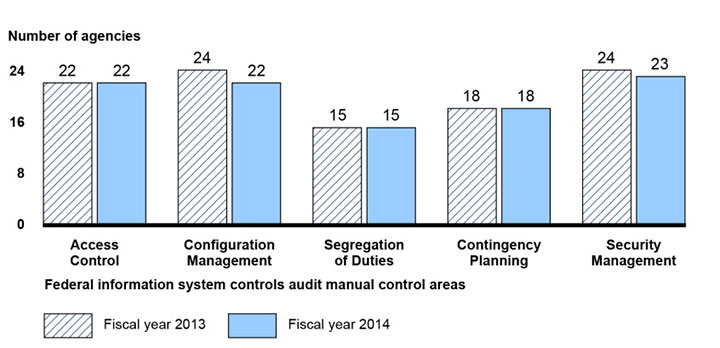
InfoSec Weaknesses at 24 Federal Agencies
Fiscal Years 2013 and 2014
Inspectors general have made hundreds of recommendations year after year to address deficiencies in IT security controls and weakness in their respective agencies' programs. "But many of these recommendations remain unimplemented," Wilshusen says.
The report is based on a review of IT security audit and guidance documents from the agencies, IGs, OMB and DHS. To assess the reliability of the documentation, GAO conducted performance audits at six agencies.
According to the report, most agencies continue to have weaknesses in:
- Limiting, preventing and detecting inappropriate access to computer resources;
- Managing the configuration of software and hardware;
- Segregating duties to ensure that a single individual does not have control over all key aspects of a computer-related operation;
- Planning for continuity of operations in the event of a disaster or disruption; and
- Implementing agencywide security management programs that are critical to identifying control deficiencies, resolving problems and managing risks continuously.
"These deficiencies place critical information and information systems used to support the operations, assets and personnel of federal agencies at risk, and can impair agencies' efforts to fully implement effective information security programs," Wilshusen says.
Inadequate Guidance
The report also provides a number of examples of the incompleteness of OMB and DHS guidance to inspectors general. For example, IGs inconsistently reported agency security performance because the guidance they received failed to include criteria for making overall risk assessments.
Clarifying OMB and DHS reporting guidance to inspectors general would enhance the quality and consistency of information reported on the status of federal agencies' implementation of information security policies, procedures and practices, Wilshusen says. "Without consistent criteria for reporting, inspectors general may be providing Congress and other oversight bodies with uneven information on the extent to which federal agencies are effectively implementing security requirements," he says.
GAO recommended that OMB, in consultation with DHS, the Chief Information Officers Council and the Council of the Inspectors General on Integrity and Efficiency, enhance reporting guidance to the inspectors general for all rating components of agency security programs, such as configuration management and risk management, so that the ratings will be consistent and comparable.
OMB concurred with the GAO's recommendations, GAO says. Information Security Media Group reached out to representatives of OMB and DHS for comment but has not received replies.