Cybersecurity Framework: Making It Work
Coordinator Discusses Role of Insurers in Setting Incentives
The Obama administration is floating the idea that the nation's critical infrastructure operators would more likely adopt voluntary IT security best practices if the government engages the insurance industry to help develop the standards and procedures in its cybersecurity framework.
See Also: Gartner® Market Guide to GRC Tools for Assurance Leaders
"The goal of this collaboration would be to build underwriting practices that promote the adoption of cyber-risk reducing measures and risk-based pricing and foster a competitive cyber-insurance market," says Michael Daniel, the White House cybersecurity coordinator.
The departments of Homeland Security, Commerce and Treasury have identified eight incentives the federal government could use to encourage the nation's critical infrastructure owners to adopt voluntarily the cybersecurity framework being developed under the auspices of the National Institute of Standards and Technology [see NIST Unveils Draft of Cybersecurity Framework].
Besides cybersecurity insurance, the seven other incentives are grants, process preferences, liability limitation, streamlined regulations, public recognition, rate recovery for price-regulated industries and cybersecurity research.
In February, President Obama issued an executive order that focused on sharing cyberthreat information, promoting online privacy protection and establishing IT security best practices, known as the cybersecurity framework, that the owners of the nation's critical infrastructure could adopt voluntarily [see Obama Issues Cybersecurity Executive Order].
NIST has been holding a series of public sessions where government and industry are developing the cybersecurity framework. NIST will hold its fourth session on the framework from Sept. 11 to 13 at the University of Texas at Dallas, where it will present a draft of the cybersecurity framework. The final version is due in February.
Promoting Risk-Reducing Measures
The Commerce Department's analysis of the cybersecurity insurance incentive says insurance carriers would bring extensive knowledge of the effectiveness of specific cybersecurity practices and could help evaluate specific proposed elements from this perspective. "This collaboration between insurance companies, NIST and other stakeholders could serve as a basis for creating underwriting practices that promote the adoption of cyber risk-reducing measures and risk-based pricing," the Commerce analysis says. "This collaboration could also foster a competitive cyber-insurance market."
Writing in the White House blog, Daniel says NIST, part of the Commerce Department, is taking steps to engage the insurance industry in further discussions on the framework.
At a Senate hearing on July 25, NIST Director Patrick Gallagher said the cyber-insurance marketplace hasn't matured to the point where large, critical infrastructure operators can transfer a significant portion of their cyber-risks to insurers. But Gallagher suggested the cybersecurity framework could help encourage that maturity [see Debating the Maturity of Cyber-Insurance].
"You need to monetize the risk; this comes down to measuring and understanding and developing an actuarial basis for this risk to be imbedded into the market," Gallagher told the senators. "This discussion has come up quite frequently in the framework process, and I think as part of the metrics discussion this is something being looked at and something that would be quite helpful."
Emerging Cyber-Insurance Market
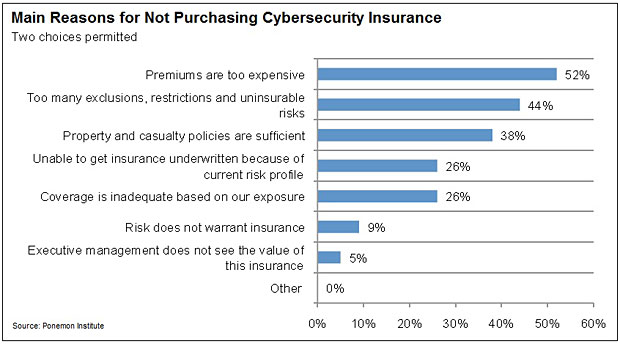
Most organizations - whether deemed critical infrastructure or not - do not carry cybersecurity insurance. A survey of chief risk officers and chief information security officers conducted by the Ponemon Institute, and released on Aug. 7, reveals that only 31 percent of companies in the United States carry cybersecurity insurance, although 39 percent of respondents say their organizations plan to purchase a policy in the next 12 months.
The reason cyber-insurance could be an incentive is the realization that it could be a vital component of an organization's risk-management strategy. "People are recognizing that security incidents are a real threat, and in terms of prudent risk-mitigation strategy, boards of directors and senior-level management are saying this is a proven part of what we should do to protect the business," says Michael Bruemmer, vice president at Experian Data Breach Resolution, a breach incident response services firm that sponsored the Ponemon study.
Among the reasons risk and security officers cite for not purchasing cybersecurity insurance: expensive premiums, too many exclusions, restrictions and uninsurable risks and inability to get insurance underwritten because of current risk profile.
Daniel says the recommendations for cybersecurity insurance as well as the other areas were created in a relatively short timeframe with the understanding they're not fully developed.
Take, for example, the incentive for liability limitation. The three departments point to a range of areas where more information is necessary to determine if legislation to reduce liability on program participants may appropriately encourage a broader range of critical infrastructure companies to implement the framework. These areas include reduced tort liability, limited indemnity, higher burdens of proof, or the creation of a federal legal privilege that preempts state disclosure requirements. As the framework is developed, agencies will continue to gather information about the specific areas identified in the reports related to liability limitation.
Encouraging Participation
In his blog, Daniel addresses other areas:
- Grants: Incentivizing the adoption of the framework and participation in the voluntary program as a condition or as one of the weighted criteria for federal critical infrastructure grants is under consideration. Over the next six months, agencies will develop such criteria for consideration.
- Process reference: Participating in the voluntary program could be a consideration in expediting existing government service delivery. As an example, Daniel points out that the government sometimes provides technical assistance to critical infrastructure. Outside of incident response situations, he says, the government could use framework adoption and participation in the voluntary program as secondary criteria for prioritizing who receives that technical assistance. "The primary criteria for technical assistance would always remain the criticality of the infrastructure, but for non-emergency situations, technical assistance could be seen as an additional benefit that could help to drive adoption," Daniel says.
- Streamline regulations: The framework and voluntary program should interact in an effective manner with existing regulatory structures. As both developed, agencies will recommend other areas that could help make compliance easier, such as eliminating overlaps among existing laws and regulation, enabling equivalent adoption across regulatory structures and reducing audit burdens.
- Public recognition: Further exploration on whether optional public recognition for participants in the program and their vendors would be an effective means to incentivize participation is under consideration. DHS will work with the critical infrastructure community to consider areas for optional public recognition.
- Rate recovery for price-regulated industries: Further dialogue with federal, state and local regulators and sector specific agencies is recommended on whether the regulatory agencies that set utility rates should consider allowing utilities to recover, through higher rates, cybersecurity investments related to complying with the framework and participation in the program.
- Cybersecurity research: Once the framework is complete, agencies should identify areas where commercial solutions are available to implement the framework and gaps where those solutions do not yet exist should be identified. The government can then emphasize research and development to meet the most pressing cybersecurity challenges where commercial solutions are not currently available.
"While these reports do not yet represent a final administration policy," Daniel says, "they do offer an initial examination of how the critical infrastructure community could be incentivized to adopt the cybersecurity framework as envisioned in the executive order."