Governance & Risk Management , HIPAA/HITECH , Incident & Breach Response
Breach Settlement Has Unusual Penalty
In Addition to $200,000 Fine, Vendor Banned From Owning or Managing a Business in New Jersey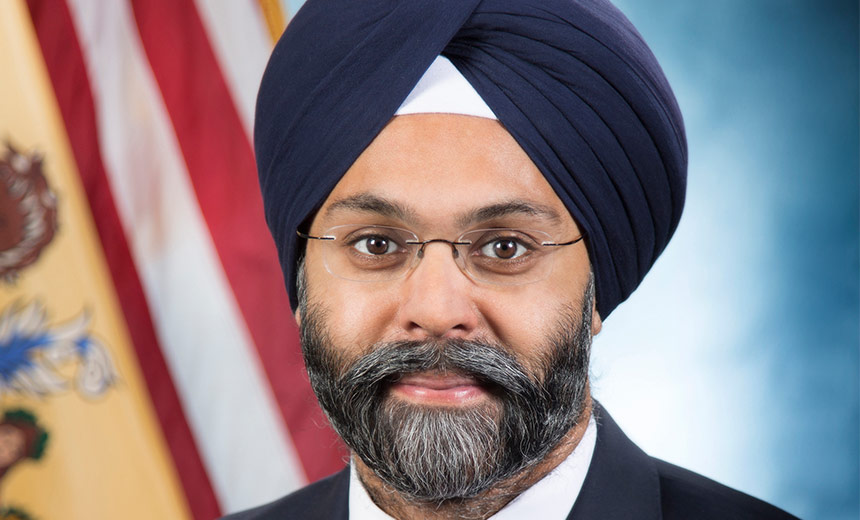
Months after the New Jersey attorney general's office smacked a medical practice with a hefty penalty for a 2016 breach, the office has signed a $200,000 settlement with the group's business associate that was responsible for the incident and banned its owner from managing or owning a business in the state.
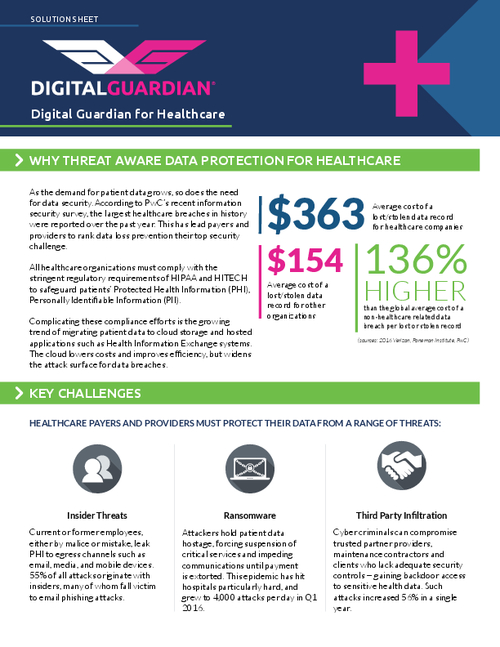
See Also: Assess, Manage and Respond to Security Risks in Heathcare
In a Nov. 2 statement, New Jersey Attorney General Gurbir Grewal said the settlement with ATA Consulting LLC, which was based in Georgia and did business as Best Medical Transcription, and its owner, Tushar Mathur, resolves allegations that the firm violated federal HIPAA regulations and the New Jersey Consumer Fraud Act in connection with a breach impacting 1,654 patients of Virtua Medical Group.
"Our action against Best Medical Transcription demonstrates that any entity that fails to comply with its duty to protect private health records of New Jersey patients will be held accountable," Grewal says.
This apparently is the first time that a state attorney general has banned a business owner from managing or owning a business in a particular state as a result of a breach settlement, says privacy attorney Iliana Peters of the law firm Polsinelli.
"While such an action may not be particularly significant for a small entity ... it could be a very big deal if taken by the state attorney general against a large entity doing business in not only the state where the action is taken, but also in other states."
—Iliana Peters, Polsinelli
"HIPAA and the HITECH Act do not provide for such actions on a federal or state level, so the state attorney general would be exercising state law specific jurisdiction to undertake such an action, which is extremely noteworthy," she says. "While such an action may not be particularly significant for a small entity such as the one that violated the HIPAA rules in this case, it could be a very big deal if taken by the state attorney general against a large entity doing business in not only the state where the action is taken, but also in other states."
Peters questions whether attorneys general across several states might "consider taking joint action to ban a particular company, in the same way they have taken joint action to resolve data security issues, including with regard to HIPAA violations."
The settlement agreement with Best Medical Transcription says that its owner, Mathur, "shall not manage or own any business in New Jersey, or serve as an officer, director, trustee, member of an executive board or similar governing body, principal, manager or stockholder owning 10 percent or more of the aggregate outstanding capital stock of all classes of any corporation in New Jersey."
In addition, the settlement says, Best Medical Transcription shall not engage in conduct in violation of the state's Consumer Fraud Act and HIPAA. But it also notes that the Mathur "has initiated proceedings for the dissolution" of Best Medical Transcription.
What Happened?
The breach at the center of the enforcement action involved a server misconfiguration that publicly exposed protected health information - including the names and medical diagnoses of patients treated by Marlton, New Jersey-based Virtua Medical Group, which reached a nearly $418,000 settlement in April for the same incident.
In that earlier settlement, the attorney general's office noted that the medical group violated multiple laws, including New Jersey's Consumer Fraud Act, as well as several provisions of the HIPAA rules, including failing to conduct an accurate and thorough risk assessment.
Documents in the new Best Medical Transcription settlement note that while the transcription firm had a business associate agreement to provide services to Virtua Medical Group, the company did not have a BA agreement with New Delhi, India-based Tojo Vikas International, the subcontractor performing transcription services for Virtua's medical practices that were impacted by the breach.

According to the settlement, from 2011 through January 2016, the affected practices submitted dictations of doctors' letters, medical notes and other reports to Best Medical Transcription through a telephone recording service. The company then uploaded the recorded .wav sound files to a password protected File Transfer Protocol site. Tojo-Vikas logged into the FTP site, listened to the sound files and transcribed the dictations into text documents, which were subsequently posted on the FTP site. To obtain the documents, personnel at the affected practices clicked a desktop icon and entered a user name and password that logged them into the FTP site. Virtua Medical Group did not have administrative access to the FTP site, but Mathur did, the settlement document says.
Around Jan. 1, 2016, the FTP site was inadvertently reconfigured by Mathur during a software update, which changed security restrictions to permit anonymous access to the FTP site, without a password needed to access the files stored, according to the settlement document.
"After the FTP site became unsecured, a web crawler from Google ... indexed the FTP site using an algorithmic process," the document says. "As a result, an individual searching Google using search terms that happened to be contained within the dictation information - patients' names, doctors' names or the affected VMG practices' names - could have obtained search results with links to the files contained on the FTP site. By clicking those links, individuals could download the complete files."
Around Jan. 15, 2016, Mathur identified that the FTP site was permitting anonymous access, and he corrected the server misconfiguration, removed the files that had been on the FTP site, and reset the password protection, the settlement document notes. Mathur's removal of the files rendered the links to those files inactive. "However ... Google retained cached indexes of the crawled files," the settlement document notes, according to the document.
Alleged Violations
In its case against Best Medical Transcription and Mathur, New Jersey's attorney general alleges a variety of HIPAA violations, including:
- Failing to conduct an accurate and thorough risk assessment of the potential risks and vulnerabilities to the confidentiality, integrity and availability of ePHI;
- Failing to implement security measures sufficient to reduce risks and vulnerabilities to a reasonable and appropriate level to comply with the HIPAA Security Rule;
- Failing to implement policies and procedures to protect ePHI from improper alteration or destruction;
- Failing to notify Virtua Medial Group of the breach of unsecured PHI;
- Improperly using and/or disclosing ePHI in violation of its obligations under its BA agreement with the medical group.
In addition, the attorney general alleges that Best Medical Transcription's HIPAA violations and the public exposure of patients' reports, "constituted separate and additional unconscionable commercial practices, in violation of the CFA [Consumer Fraud Act]," the document notes.
Noteworthy Settlement
This case is noteworthy for several reasons, including the state attorney choosing to take action against both the covered entity and business associate involved with the breach, but also for the enforcement action against the BA's owner.
"The attorney general of New Jersey has an array of penalties and relief to enforce the state's Consumer Fraud Act, including fines and suspension or revocation of authority against a company or individual to do business in the state," says privacy attorney David Holtzman, vice president of security compliance at the consultancy CynergisTek.
"While it is not uncommon for a negotiated settlement agreement to include a period of exclusion for a company or its officers, this the first time I am aware of the New Jersey attorney general applying this in relation to an investigation regarding unauthorized disclosure of health information. "
There have been a handful of similar actions by state and federal regulators in other cases involving data security, he notes.
"In 2012, the state of Minnesota banned Accretive Health from doing business in the state for two years over its hospital billing and debt collection practices that also included the theft of an unencrypted laptop from an employee's car that held the PHI of several Minnesota hospitals," Holtzman notes.
And in 2014, the Federal Trade Commission, using its authority to enforce prohibition of unfair trade practices, banned the CEO of medical billing company PaymentsMD "from deceiving consumers in order to obtain their personal information to settle allegations that they misled patients in the collection of health data," he notes.
Other breach-related cases have involved medical transcription service providers and their management of subcontractors, Holtzman points out.
In 2014, the FTC entered into a consent agreement with GMR Transcription in a case involving a misconfigured FTP site that allowed sensitive health information belonging to several dozen physician practices to be viewable on the internet, he notes.
"The common thread ... is that the U.S. based transcription vendor subcontracted with offshore transcriptionists. In both cases, the HIPAA covered entities had fulfilled their HIPAA obligations to have BA agreements in place with their vendor," he says. "And unbeknownst to the covered entity, their vendor was relying on subcontractors to safeguard their PHI."
HHS Actions
Officials at the Department of Health and Human Services' Office for Civil Rights, which enforces HIPAA, have announced on several occasions that HHS does not make it a practice to put healthcare entities out of business, notes Peters, a former OCR official.
OCR, however, has entered into settlement agreements and imposed civil monetary penalties against entities that were in the process of dissolving - including earlier this year in a breach case involving now-defunct records storage firm Filefax, Peters notes.
"It's also important to consider that the Centers for Medicare and Medicaid Services does include data privacy and security protections in their conditions for participation, and the Office of the National Coordinator requires attestation regarding data security requirements for certification of electronic health records systems," Peters adds. "As such, on some level, CMS and ONC could both exclude or delist, respectively, entities that do not fulfill their requirements under those conditions, as well."
HIPAA covered entities and business associates, as well as all types of entities doing business with consumer data, must understand that both federal and state authorities "continue to take action that evidences serious commitment to ensuring that such entities undertake good data security, and that these authorities have, and will likely use, all of the tools available to them to ensure that consumers are protected in that regard," Peters stresses.