Breach Lawsuits: Why Winning Is Tough
Another Advocate Health Breach Suit Dismissed
Recent court dismissals of two class action lawsuits related to an Advocate Health Care 2013 data breach impacting 4 million individuals are a reminder of how difficult it can be for plaintiffs to prevail in cases where there is no evidence of damages, such as fraud or identity theft.
See Also: Embracing Digital Risk Protection: Take Your Threat Intelligence to the Next Level
One healthcare privacy attorney, however, says that long-overdue federal regulations called for under the HITECH Act, which would define "harmed individuals" who might qualify for payments from HIPAA-violation penalties collected by regulators, could potentially impact how courts rule on breach litigation.
On July 10, Kane County, Ill., Circuit Court Judge James Murphy dismissed a class action suit filed against Advocate last October. The suit was filed the wake of the July 2013 theft of four unencrypted computers from a Chicago-area Advocate physicians' office, which may have exposed information on 4 million patients.
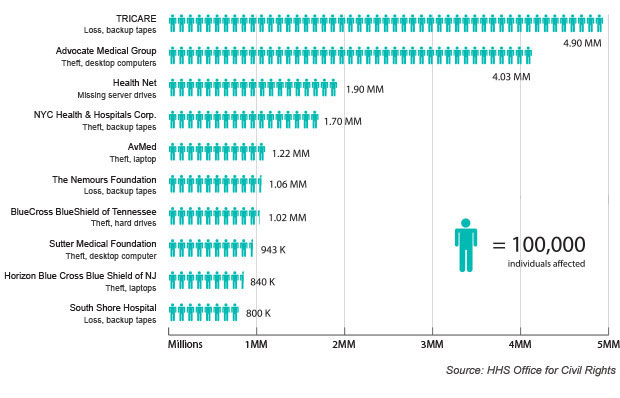
The suit alleged the incident, which is the second largest listed on Department of Health and Human Services' "wall of shame" website of major breaches, put the patients at risk for fraud.
That court decision closely follows the dismissal in May of a similar class action suit against Advocate that was filed last year in Lake County, Ill. Circuit court. That case against the healthcare provider was also dismissed because there was no evidence of identity theft or fraud as a result of the theft. A hearing to reconsider that Lake County ruling is set for Sept. 3.
Matt Herman, an attorney of law firm Foote Mielke Chavez & O'Neil LLC, which is representing the plaintiffs in the Kane County case that was dismissed last week, declined to comment on the ruling.
In addition to the two dismissed cases, several other similar class action lawsuits are still pending against Advocate, including a lawsuit filed in federal court and a consolidation of about a dozen class action suits filed in Cook County, Ill. (see: Lawsuit Filed In Advocate Medical Breach).
In reference to the ruling last week in Kane County, Advocate told Information Security Media Group in a statement, "There was no indication in this case that patient information was misused and accordingly, the court dismissed the case. Protecting the privacy of our patients continues to be a top priority at Advocate Health Care."
Other High-Profile Cases
The recent dismissal of the Advocate suits follows similar court decisions in other high-profile breach cases. The largest includes a ruling by a federal district judge in May dismissing the majority of a consolidated class action lawsuit that was filed against TRICARE, the military health program, and Science Applications International Corp. in the wake of a 2011 data breach that affected nearly 5 million individuals. That incident is the largest data breach reported to federal regulators under the HIPAA breach notification rule.
Of the 33 plaintiffs in the eight class action lawsuits that were consolidated, only two "do plausibly assert that their data was accessed or abused, and those victims may move forward with their claims," wrote U.S. District Judge James Boasberg in his May 9 ruling (see Most Claims in TRICARE Breach Dismissed).
Ten Largest Health Data Breaches
With a few exceptions, so far, most class action suits related to health data breaches haven't proceeded very far in court, notes attorney Linn Freedman, a partner at Nixon Peabody LLP in Rhode Island, and leader of its privacy and data protection group. "In general, these cases are being handled like other data breaches where plaintiffs must show actual compensable damages in order to prevail beyond a motion to dismiss," she says.
Among recent exceptions was a recent ruling by the West Virginia Supreme Court related to a class action suit filed against Charleston Area Medical Center in the wake of a 2011 breach.
"The West Virginia case was unusual," Freedman says. In that case, a lower court denied class certification because the plaintiffs were unable to show any actual or imminent "concrete, particularized injury" related to the breach, Freedman says. However, in May, the state's Supreme Court reversed the lower court's decision to deny class certification for individuals notified of the data breach. In its ruling, the Supreme Court wrote that it agreed with the plaintiffs' class certification argument that, "the petitioners alleged ... that the respondents [medical center] are responsible for placing the petitioners' personal and medical information on a specific ... electronic database and website which was accessible to the public."
The Supreme Court, however, did not rule on the merits of the plaintiffs' case: "This court makes absolutely no determination regarding the merits or the lack thereof of the petitioners' causes of action for breach of confidentiality and invasion of privacy, such as whether the petitioners have adduced evidence sufficient to prove the elements of these causes of action. "
Charleston Area Medical Center did not respond to ISMG's request for comment on the case.
Another exception to a trend of class action lawsuits being dismissed when there's no evidence of damages is the $3 million settlement last year by AvMed, a Florida-based health insurer, stemming from a 2009 data breach involving the theft of two unencrypted laptop computers containing data on 1.2 million individuals (see Settlement in AvMed Breach Suit).
The AvMed settlement, filed in a U.S. District Court, is considered significant because it awarded payments to individuals who were not victims of identity theft, but who paid premiums to AvMed in years leading up to the theft).
Settlement documents in that case explain that awards of up to $30 each to about 460,000 individuals affected by the breach represents what AvMed should have spent on protecting data, amounting to a refund of premium overpayment.
Additionally, individuals who were victims of identity theft as a result of the breach can submit claims to be reimbursed by AvMed for their monetary losses.
Changes Ahead?
Privacy attorney Adam Greene, a partner with the Washington law firm David Wright Tremaine, says the recent Advocate rulings "fit with the general trend that we have seen of courts dismissing breach cases due to lack actual harm and, therefore, a lack of standing."
But besides the AvMed settlement and recent West Virginia ruling, "California is [another] major exception in the health care space, since the California Confidentiality of Medical Information Act provides for nominal damages of $1,000 per person when actual harm cannot be demonstrated," he notes.
Looking ahead, lawsuits filed in the wake of health data breaches could be influenced by other factors, he says. "One major potential change on the horizon is that the HITECH Act requires HHS to issue regulations providing for distribution of a portion of settlements and fines to harmed individuals" in HIPAA breaches, he says. "We have not yet seen a proposed rule on this issue. A federal definition of who is a 'harmed individual' could impact state courts' interpretation of whether individuals have been harmed and have a basis to proceed with a lawsuit."
So, for instance, if potential HHS regulations state there must be evidence of financial damages for "harmed individuals" to receive a portion of HIPAA enforcement settlements collected by HHS' Office for Civil Rights, then it could become more difficult for plaintiffs to also pursue these suits in state courts if there is no evidence of financial harm, he says.
But it's not clear when HHS might get around to proposing those regulations. "The [HITECH] statute called for regulations by February 2012. I have not heard OCR talk about these regulations much at all and don't get the impression that this is one of their priorities compared to publishing the HIPAA Omnibus guidance," Greene says.
OCR did not respond to ISMG's request for comment on the status of any potential new regulations that might get proposed.