Access Management , Cybercrime , Fraud Management & Cybercrime
Attacks Using LokiBot Information Stealer Surge
CISA Alert Notes Malware Is Targeting Victims' Credentials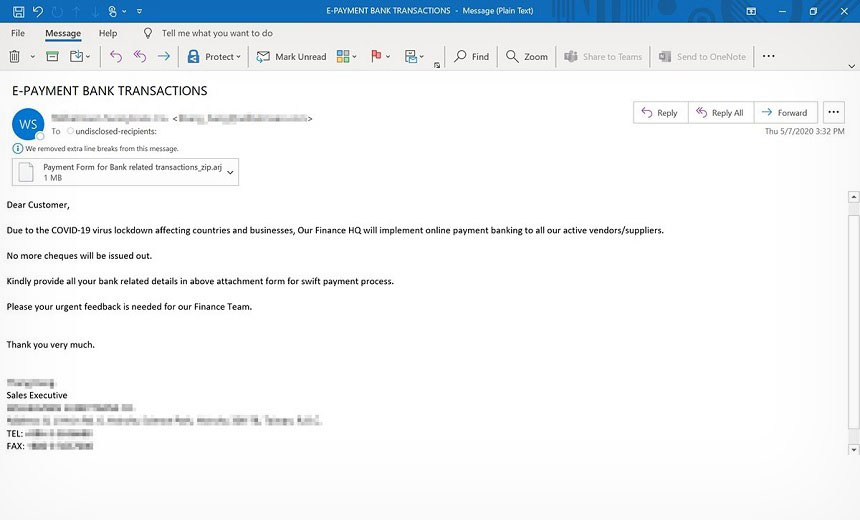
The U.S. Cybersecurity and Infrastructure Security Agency is warning of an uptick in attacks using LokiBot, an information stealer capable of sweeping up credentials.
See Also: Cybersecurity for the SMB
In a Tuesday alert, CISA notes that attacks using LokiBot have steadily increased since July. Earlier, Microsoft noted in an analysis that fraudsters were using this malware variant in phishing emails that contain a COVID-19 theme (see: Fresh Twist for Pandemic-Related Phishing Campaigns ).
CISA notes that its intrusion detection and prevention program, known as Einstein, had been picking up an increasing amount of malicious activity using LokiBot malware.
LokiBot is “known for being simple, yet effective, making it an attractive tool for a broad range of cyber actors across a wide variety of data compromise use cases," according to CISA.
Earlier this month, Finnish security firm F-Secure noted that of all the COVID-19-themed malicious emails that it examined in the first half of this year that used attachments, 75% deployed either LokiBot or Formbook (see: Cybercrime Review: Hackers Cash in on COVID-19 ).
F-Secure also noted that the most common type of malware the company discovered in the first half of this year was information stealers, and the most prevalent of these was LokiBot.
LokiBot Capabilities
Lokibot, which is also known as Loki PWS, has been active since 2015. The information stealing Trojan was initially spread through malicious email attachments.
Since July, however, attackers have been using a wider range of tactics to spread the malware, CISA says. These include using malicious websites that hide the malware from victims as well as sending phishing links through SMS and other private messages that contain LokiBot.
Once a device is compromised, the malware uses a keylogger to steal stored passwords and credentials in victims' web browsers as well the device itself, according to CISA. In addition to data exfiltration, LokiBot acts as a backdoor to download other malicious payloads.
CISA notes LokiBot comes with capabilities to exfiltrate a wide range of data, including credentials for cryptocurrency wallets.
Other security firms have noted a steady increase in fraudsters using LokiBot. In April, for example, hackers used official images and other trademarks of the World Health Organization as a lure to spread LokiBot, according to FortiGuard Labs (see: Spear-Phishing Campaign Uses COVID-19 to Spread LokiBot).
Threat to Remote Workforce
Because the malware is capable of stealing a wide range of data, security experts note a potential LokiBot attack on an organization, especially on its remote workforce, can have grave repercussions.
"If a workstation gets infected with LokiBot or similar malware, an organization may find it extremely difficult to kick out the attackers and keep them out," Zach Varnell, senior consultant at security firm nVisium, tells Information Security Media Group. "This threatens remote workers as well, since a compromise could easily result in attackers gaining valid credentials for cloud services, collaboration software and other tools used to keep remote teams connected."
Brandon Hoffman, CISO at security firm Netenrich, says organizations that switched to a remote workforce without implementing adequate security controls would be the ideal target for the LokiBot-wielding attackers.
"Security controls are somewhat limited when the entire workforce remains remote,” he says.
Risk Mitigation
The CISA report outlines steps organizations can take to help prevent attacks using LokiBot, including:
- Maintain up-to-date anti-virus signatures and engines;
- Keep operating system patches up to date;
- Disable file and printer sharing services. If these type of services are needed, organizations should use strong passwords or Active Directory authentication;
- Enforce multifactor authentication for employees to access PCs and other devices;
- Require a firewall to access certain workstations and other devices.